Ice Tube Clock Kit
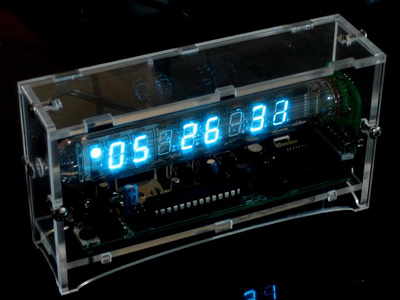
This clock kit by Adafruit is made with a retro Russian display tube!
* Cool glowing blue tube with 8 digits, PM dot and alarm on/off indicator
* Adjustable brightness
* Alarm with volume adjust
* Precision watch crystal keeps time with under 20ppm (0.0002%) error (< 2 seconds a day)
* Clear acrylic enclosure protects clock from you and you from clock
* Battery backup will let the clock keep the time for up to 2 weeks without power
* Selectable 12h or 24h display
* Displays day and date on button press
* 10 minute snooze
* Integrated boost converter so it can run off of standard DC wall adapters, works in any country regardless of mains power
* Great for desk or night table use, the clock measures 4.9" x 2.9" x 1.3" (12.5cm x 7.4cm x 3.3cm)
* Completely open source hardware and software, ready to be hacked and modded
